Mad lad stores and loads Doom from within DNS — TXT record type abused to store game data
You should grab a stiff drink before reading this.
Get 3DTested's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Network administrators in the audience are advised to grab their unsee juice from the shelf, as today's home project is quite the double-whammy. First, it involves everyone's favorite problem child, DNS. Second, a madlad named Adam Rice has managed to put Doom in it. That's a paragraph I never thought I'd write, but my life choices haven't always resulted in glory.
For the uninitiated, every time you go to tomshardware.com, your device first asks a server what its actual numerical address is. That's DNS, or Domain Name System, and it's the cornerstone of the internet. Rice appears to be an expert at bending DNS into four-dimensional shapes, like abusing its TXT records to deliver malware payloads.
As the acronym implies, a TXT record contains a string of text. They're normally used for domain validation and spam control, and you tend to need maybe a half-dozen for most any domain. The thing is, they can contain arbitrary data by definition. And as Rice points out, where you can store data, you can store a file, and therefore a program like Doom.
Article continues belowTXT records can contain up to 2,000 characters, and any single domain can have thousands of records. And since DNS entries are cached in many layers across the entire internet, that means you can store a substantial amount of data and query it at a relatively decent pace. Developers in the crowd probably already know where this is heading.
Rice first thought of storing a simple file, in this case a picture of a duck, by encoding the binary data into text-readable base64 format, cutting it into many slices as needed, since transforming to text incurs significant overhead. He considering trying a movie next, but even 1 GB of data would take 670,000 records, so he settled on "something that would actually demonstrate how absurd this is": Doom, of course
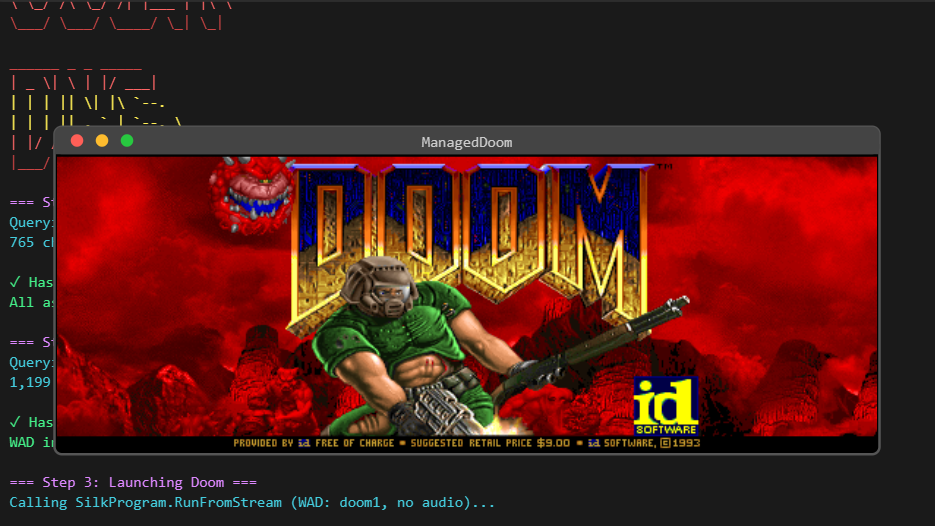
Rice needed an easy way to de- and reassemble Doom from DNS records into memory, and so he used a C# port of the game called managed-doom. C# is a bytecode language, meaning that the source code is first compiled to a cross-platform binary, which then is run in the.NET engine that does the final translation to the target CPU's instructions; all of this in a manner similar to Java.
Since Rice wanted to completely avoid writing files to disk, he employed the virtual hand of the Claude bot for tweaking parts of the game's loading process to read all data from memory. He deleted the audio files as they took up too much space, but after some compression wizardry, he managed to squeeze the game in about 3.8 MB spread across 2,000 DNS records.
Get 3DTested's best news and in-depth reviews, straight to your inbox.
With the hardest work performed, he wrote a loading script in PowerShell that queries one of his domains for TXT records, reassembles the data, and verifies against any corruption. At that point, all the game's contents are in memory, and it's just a matter of starting it like any other.NET program.
Rice describes his projects as "cursed," and I have to concur — Cloudflare's DNS servers are probably going to need trauma counseling afterwards. The project is on GitHub if you want to follow in Rice's footsteps.

Follow 3DTested on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.
